You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
Copy file name to clipboardExpand all lines: en/developer/overview.mdx
+1-1Lines changed: 1 addition & 1 deletion
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -36,7 +36,7 @@ Visit the [API documentation](https://developer-en.flashcat.cloud/en/flashduty/o
36
36
37
37
## MCP Server
38
38
39
-
The Flashduty MCP Server implements the [Model Context Protocol](https://modelcontextprotocol.io/), providing AI tools with 16 tools across 6 functional modules:
39
+
The Flashduty MCP Server implements the [Model Context Protocol](https://modelcontextprotocol.io/), providing AI tools with 18 tools across 6 functional modules:
The active alerts page provides a consolidated view of all currently firing alerts, helping you quickly understand the overall alert status of your system. You can filter and browse by severity, folder, alert rule, labels, and more.
7
+
The active alerts page provides a consolidated view of all currently firing alerts, helping you quickly understand the overall alert status of your system. You can filter and browse by severity, title, labels, and more.
8
8
9
9
<Note>
10
10
The active alerts feature requires monit-edge version >= v0.36.0. Please ensure you have upgraded to this version or later. If you have not installed it yet, go to the [alert engine management](/en/monitors/engine/engine) page to complete the deployment.
@@ -20,18 +20,22 @@ The active alerts list displays currently firing alerts in a table format. Defau
20
20
|--------|-------------|
21
21
|**Severity**| The severity level of the alert: Critical, Warning, or Info |
22
22
|**Title**| The title of the alert event |
23
-
|**Alert rule**| The name of the alert rule that produced this alert |
24
-
|**Labels**| Label information carried by the alert, such as job, instance, etc. |
25
-
|**Last triggered**| The most recent time this alert was triggered |
23
+
|**Job**| The job label value carried by the alert |
24
+
|**Instance**| The instance label value carried by the alert |
25
+
|**Last updated**| The most recent time this alert was updated |
26
+
|**Hash**| The unique identifier hash of the alert |
27
+
|**Extra labels**| Other additional label information carried by the alert |
26
28
27
29
## Filtering and searching
28
30
29
31
The conditions bar at the top of the page helps you quickly locate the alerts you care about:
30
32
31
33
-**Severity**: Filter by Critical, Warning, or Info
32
-
-**Folder**: Filter by the folder that the alert rule belongs to
33
-
-**Alert rule**: Filter by a specific alert rule
34
-
-**Labels**: Filter by alert label key-value pairs
34
+
-**Title**: Filter by the title of the alert event
35
+
-**Hash**: Filter by the unique identifier hash of the alert
36
+
-**Job**: Filter by the job label value
37
+
-**Instance**: Filter by the instance label value
38
+
-**Extra labels**: Filter by other additional labels
35
39
36
40
All filter conditions use an "AND" relationship — only alerts matching all conditions are displayed.
Copy file name to clipboardExpand all lines: en/monitors/faq/faq.mdx
-1Lines changed: 0 additions & 1 deletion
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -29,7 +29,6 @@ The overview page provides a global view of alert rules, consisting of the follo
29
29
|------|-------------|
30
30
|**Alert rule total trend**| An area chart showing how the total number of alert rules changes over time. The x-axis represents dates and the y-axis represents rule count, helping you track overall growth or reduction trends |
31
31
|**Alert rules by channel**| A pie chart showing the distribution of alert rules across channels. The top 10 channels are displayed by default; the remainder are aggregated as "Others." You can click to expand and view all details |
32
-
|**Triggered rules by top-level group**| Shows the health status of alert rules by top-level group. Each group displays as a card with a "normal/total" ratio and progress bar. Green indicates all normal; red indicates rules currently triggered. Click a card to jump to that group's rule list |
33
32
|**System event list**| Displays system events generated by the alert engine (such as engine disconnection, configuration anomalies, etc.), with pagination and delete support, helping you promptly discover and address infrastructure-level issues |
Copy file name to clipboardExpand all lines: en/monitors/quickstart/quickstart.mdx
+4Lines changed: 4 additions & 0 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -95,6 +95,10 @@ If you need stable rule bindings that are unaffected by data source renames, pre
95
95
96
96
Configure how to query data sources and how to evaluate alert conditions. Please read the usage instructions on the right side of **Query Detection Method** on the page.
97
97
98
+
| Config Item | Description |
99
+
|--------|------|
100
+
|**Query Offset**| Sets the query time offset (in seconds) to handle data source ingestion lag. For example, setting it to 60 shifts the query window back by 60 seconds, ensuring data has been fully written before querying |
101
+
98
102
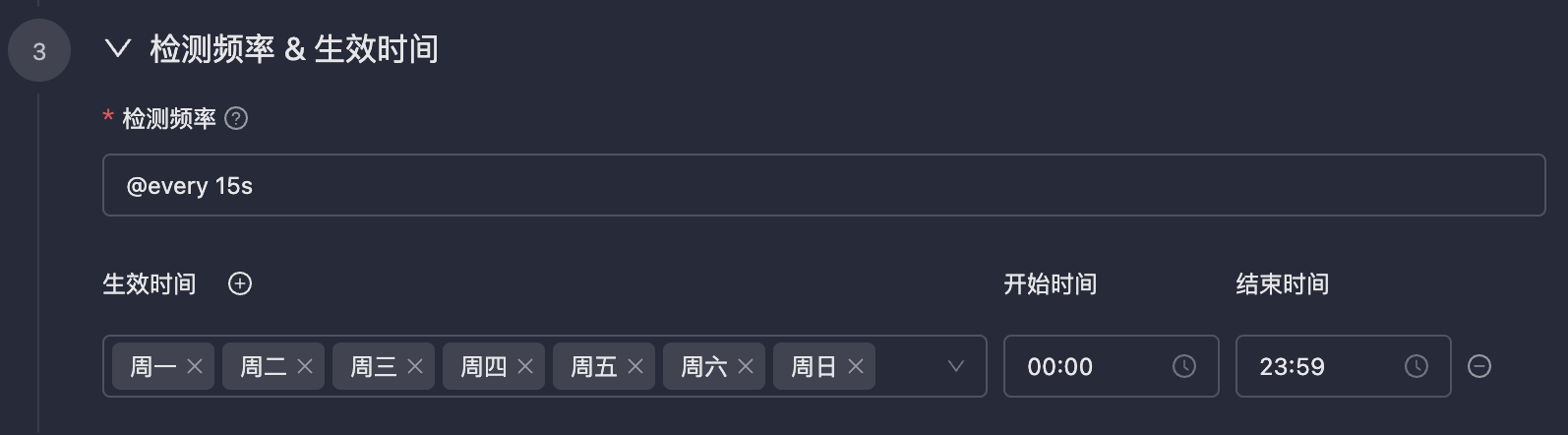
### Detection Frequency and Effective Time
99
103
100
104
An escalation rule contains four core elements. The system matches rules from top to bottom, **stopping after the first successful match**.
22
22
23
+
You can enable or disable individual escalation rules. Disabled rules are skipped during matching and will not trigger notifications. You can also copy an escalation rule to the current channel or another channel to quickly reuse existing configurations.
24
+
23
25
### 1. Trigger Conditions
24
26
25
27
Determines which incidents trigger the current rule.
@@ -88,8 +90,8 @@ In each escalation level, you can enable the **Loop Notification** feature. When
88
90
89
91
**Escalation Conditions**:
90
92
91
-
-**Timeout without acknowledgment**: No one acknowledges within N minutes after incident trigger
92
-
-**Timeout without closure**: Incident not resolved within N minutes after trigger
93
+
-**Not closed**: Incident not closed within N minutes after trigger
94
+
-**Not closed and not acknowledged**: Incident neither closed nor acknowledged within N minutes after trigger
Copy file name to clipboardExpand all lines: en/on-call/channel/noise-reduction.mdx
+2-1Lines changed: 2 additions & 1 deletion
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -104,7 +104,7 @@ Flashduty On-call provides two grouping modes:
104
104
|**Aggregation Window**| Optional toggle. When disabled, new alerts continue merging into the incident until the incident is closed. When enabled, alerts within the window are merged; alerts arriving after the window expires are grouped into a new incident |
105
105
|**Window Timing Start**| Only configurable when the aggregation window is enabled. **Incident trigger** (default): Fixed timer starts from incident creation, stops grouping when the window duration is reached. **Alert merges into incident**: Timer resets each time a new alert merges in, the window recalculates from the last merge |
106
106
|**Window Duration**| Only configurable when the aggregation window is enabled. Set the duration of the aggregation window |
107
-
|**Alert Storm Warning**| When merged alert count reaches the configured threshold, the system records an alert storm event in the incident timeline and triggers a warning notification, prompting urgent handling |
107
+
|**Alert Storm Warning**| When merged alert count reaches a configured threshold, the system records an alert storm event in the incident timeline and triggers a warning notification, prompting urgent handling. You can configure up to 5 thresholds, each ranging from 2 to 10,000|
108
108
|**Strict Grouping**| When enabled, empty label values are treated as different; when disabled, empty values are treated as the same (not supported for intelligent grouping) |
109
109
110
110
<Tabs>
@@ -234,6 +234,7 @@ Define which alerts should be silenced, supports multiple condition combinations
234
234
|**Severity**| Match by alert level | Only silence `Info` level |
235
235
|**Title**| Match by alert title keywords | Title contains "Planned Maintenance" |
236
236
|**Description**| Match by alert description content | Description contains "restart" |
237
+
|**Integration**| Match by alert integration source | Only silence alerts from a specific integration |
237
238
|**Labels**| Match by label key-value pairs |`host=db-master-01`|
Copy file name to clipboardExpand all lines: en/on-call/incident/search-view-incident.mdx
+1-1Lines changed: 1 addition & 1 deletion
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -137,7 +137,7 @@ The incident details page supports one-click AI summary generation to help you q
137
137
-**Impacts**: Key affected resources such as services, systems, environments, and instances
138
138
-**Actions**: Immediately actionable investigation and remediation steps (up to 3)
139
139
140
-
You can choose from different AI models (default is DeepSeek V3) and regenerate as needed. The generated summary supports real-time streaming output and can be saved as the incident description.
140
+
You can choose from different AI models (default is DeepSeek V3; DeepSeek R1 is also available for deep thinking and reasoning capabilities) and regenerate as needed. The generated summary supports real-time streaming output and can be saved as the incident description.
141
141
142
142
<Tip>
143
143
AI Summary is only available for incidents automatically triggered by alerts. Manually created incidents do not support this feature.
Copy file name to clipboardExpand all lines: en/on-call/integration/alert-integration/alert-pipelines.mdx
+4Lines changed: 4 additions & 0 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -114,6 +114,10 @@ Pipeline's inhibition feature is similar to channel inhibit rules, both supporti
114
114
When an entire datacenter loses network, all alerts from that datacenter (regardless of business line) should be inhibited. Configuring one rule at the integration layer is much more efficient than configuring separately in dozens of channels.
115
115
</Tip>
116
116
117
+
<Note>
118
+
Inhibition only matches source alerts that have been active within the last 10 minutes (600 seconds). If a source alert was triggered more than 10 minutes ago and has not been updated since, it will not be used for inhibition matching. Ensure your source alerts remain active within this time window.
119
+
</Note>
120
+
117
121
## Reference Historical Data
118
122
119
123
When editing alert processing rules, the right side of the page provides a **Related Alerts** panel showing historical alert data ingested through the current integration. You can write processing rules while referencing actual alert content, ensuring that condition expressions and action configurations meet expectations.
Copy file name to clipboardExpand all lines: en/on-call/integration/instant-messaging/microsoft-teams.mdx
+15-2Lines changed: 15 additions & 2 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -121,7 +121,20 @@ In the Chat, @Flashduty and send command `linkChat {ID} {ChatName}`, then click
121
121
</Step>
122
122
</Steps>
123
123
124
-
## 4. Link User
124
+
## 4. Notification Card Actions
125
+
126
+
When incident notifications are pushed to Microsoft Teams, the notification cards support the following interactive actions, allowing you to respond to incidents directly in Teams without switching to the Flashduty console:
127
+
128
+
-**Acknowledge**: Mark that you have started handling the incident
129
+
-**Resolve**: Mark the incident as resolved and close it
130
+
-**Snooze**: Temporarily suspend the incident and receive a reminder after a specified time
131
+
-**Custom Actions**: Trigger your pre-configured custom actions (such as restarting services, rolling back changes, etc.)
132
+
133
+
<Note>
134
+
War room functionality is not currently supported for Microsoft Teams. If you need to use the war room feature, consider using Slack, Feishu/Lark, Dingtalk, or WeCom integration instead.
135
+
</Note>
136
+
137
+
## 5. Link User
125
138
126
139
<Steps>
127
140
<Steptitle="Find App">
@@ -147,7 +160,7 @@ Copy and send command `linkUser {}` to the chat, then click **Link Now**.
147
160
</Step>
148
161
</Steps>
149
162
150
-
## 5. FAQ
163
+
## 6. FAQ
151
164
152
165
<AccordionGroup>
153
166
<Accordiontitle="Team or individual not receiving messages?">
Copy file name to clipboardExpand all lines: en/on-call/integration/instant-messaging/slack.mdx
+7-15Lines changed: 7 additions & 15 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -33,21 +33,6 @@ After completing the previous steps, in the Flashduty On-call integration config
33
33
To enable AI-generated post-mortem with war room chat history, the app requires additional `channels:history` permission. For existing Slack integrations, you need to manually re-authorize to grant this permission.
34
34
</Note>
35
35
36
-
## 3. FAQ
37
-
<Warning>
38
-
Only one IM integration can have War Room enabled at a time. If you've already enabled War Room in another IM integration (such as Dingtalk, Feishu/Lark, or WeCom), you need to disable it there first before enabling it in the current Slack integration.
39
-
</Warning>
40
-
41
-
### Permission verification and re-authorization
42
-
43
-
When enabling War Room, the system automatically verifies whether the current Slack app has all the permissions required for War Room. If missing permissions are detected, a warning message appears on the page with a **Re-authorize** link.
44
-
45
-
Click the **Re-authorize** link to be redirected to the Slack authorization page, which requests the additional permissions needed for War Room functionality (including channel management, message read/write, user info reading, etc.). After completing authorization, the page automatically returns to Flashduty, and you can then enable War Room normally.
46
-
47
-
<Tip>
48
-
If your Slack integration was authorized before the War Room feature was released, you will typically need to re-authorize on first use to add the new permissions. Re-authorization does not affect your existing integration configuration or user associations.
49
-
</Tip>
50
-
51
36
## 3. Linked Users
52
37
53
38
In the **Linked Users** tab of the integration detail page, you can view the linking status between team members and Slack accounts, and quickly complete batch linking.
@@ -75,6 +60,13 @@ The system can only push Slack message notifications after members complete link
75
60
## 4. FAQ
76
61
77
62
<AccordionGroup>
63
+
<Accordiontitle="War Room considerations?">
64
+
- Only one IM integration can have War Room enabled at a time. If you have already enabled War Room in another IM integration (such as Dingtalk, Feishu/Lark, or WeCom), you need to disable it there first before enabling it in the current Slack integration
65
+
- When enabling War Room, the system automatically verifies whether the current Slack app has all required permissions. If missing permissions are detected, a warning message appears on the page with a **Re-authorize** link
66
+
- Click the **Re-authorize** link to be redirected to the Slack authorization page, which requests additional permissions needed for War Room functionality (including channel management, message read/write, user info reading, etc.). After completing authorization, the page automatically returns to Flashduty
67
+
- If your Slack integration was authorized before the War Room feature was released, you will typically need to re-authorize on first use to add the new permissions. Re-authorization does not affect your existing integration configuration or user associations
68
+
</Accordion>
69
+
78
70
<Accordiontitle="Escalation rule group chat list doesn't have the desired private channel?">
79
71
- Ensure the [**Install App**](#install-app) step completed successfully without errors
80
72
- Go to the relevant Slack channel, execute `/invite @Flashduty` command
0 commit comments